In the last 2 days I worked full-time to help a company fix their site which was getting hacked continuously over and over!
The situation was pretty out of control and the hosting company was very supportive but was just “rebuilding” the site with backups. As you may know, doing just that won’t take you very far. In reality, removing malware is not their job and they could not offer this service which usually needs a dedicated service.
This is a security issue that needed a professional approach , as the platform itself was “ok” from a WordPress point of view: The CMS installed was the latest version and also most of the “core” plugins were updated, but all WordPress sites need a proper installation and some extra measures that only a professional developer or company can implement.
So where did the “menace” come from and how did it break through the site?
There were so many factors involved and a lot of files and backdoors installed that I took a quite an extreme approach: Examine the site from the root key files till the last image file that could “hide” a backdoor. The site also had WooCommerce installed along with orders and we could not take any unnecessary risks.
It was a very time-consuming task! There is no magic recipe that will clean and secure your site, and the same approach doesn’t always work.
The hackers were able to log into the site because of a vulnerable set-up and a theme. Also some theme-connected plugins were not updated correctly which could lead to a backdoor that was able to inject into the site a file that self extracted to create a new “site” into the website. This was like a full new site with proper functional email that was bombing around and creating Scam and False sites into the subdirectories!
This site also was continuously under attack with brute force and SQL injection attempts.
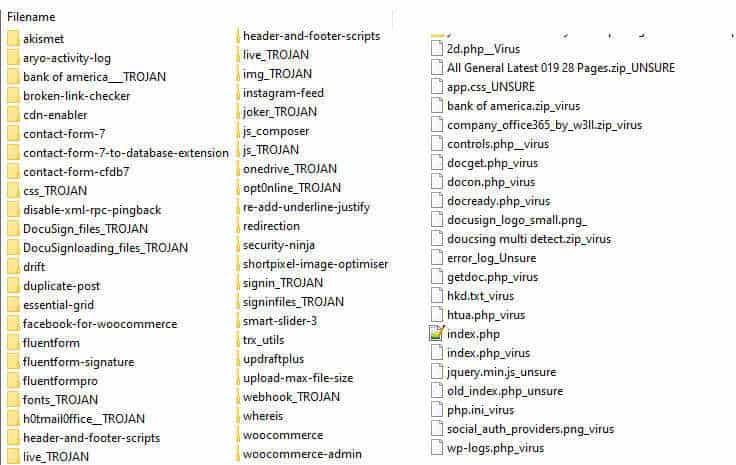 After Checking the “fake” directories and the Trojan ones, plus the virus files we also had to secure the data.
To avoid that any potential virus files would break the site, I had to test one by one the folders into the plugins dir to make sure it won’t lead to any further damage.
Also, I had to cut the “loop” where the site was continuously re-attempting to create the dirs and the backdoor over and over, which kept getting the site “hacked”.
It was No Joke!
Lastly, we had to troubleshoot the WP-ADMIN dashboard as some functions were corrupted and some buttons were not fully operational leading to a broken admin dashboard.
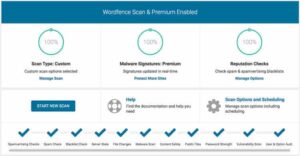
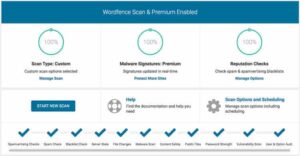
Updating the site theme along with some extra security measures and installation of a WP security plugin helped the site to have a ZERO downtime and a full recovery.
We had to keep it under testing and we’re still doing it now but, fingers crossed, I was able to avoid a complete “rebuilt” of the site or, more importantly, loss of precious, valuable data.
After Checking the “fake” directories and the Trojan ones, plus the virus files we also had to secure the data.
To avoid that any potential virus files would break the site, I had to test one by one the folders into the plugins dir to make sure it won’t lead to any further damage.
Also, I had to cut the “loop” where the site was continuously re-attempting to create the dirs and the backdoor over and over, which kept getting the site “hacked”.
It was No Joke!
Lastly, we had to troubleshoot the WP-ADMIN dashboard as some functions were corrupted and some buttons were not fully operational leading to a broken admin dashboard.
Updating the site theme along with some extra security measures and installation of a WP security plugin helped the site to have a ZERO downtime and a full recovery.
We had to keep it under testing and we’re still doing it now but, fingers crossed, I was able to avoid a complete “rebuilt” of the site or, more importantly, loss of precious, valuable data.
 I was pleased to also receive very positive feedback from the hosting company itself regarding my work, which was appreciated and recognized as a valuable one.
As a bonus, we also had the email address that was receiving the data from the Scam-Created site along with the Hacking team connected (maybe… this info is never trustworthy as there are internal rivalries) and reported to whom it concerns for further investigation.
A few steps that I followed:
I was pleased to also receive very positive feedback from the hosting company itself regarding my work, which was appreciated and recognized as a valuable one.
As a bonus, we also had the email address that was receiving the data from the Scam-Created site along with the Hacking team connected (maybe… this info is never trustworthy as there are internal rivalries) and reported to whom it concerns for further investigation.
A few steps that I followed:
 WordPress is a very complete, complex and still easy platform to work with that can provide professional results with a few clicks and free plugins. Many people think that for this reason, it’s “ok” to get the job done by themselves or with a cheap company.
A professional removal service tailored like this one I did costs a lot of money, between 500 and 1.5k, and it’s not always guaranteed that the results will be 100% accurate …
So think first about it when you want to cut costs on security.
I would say that getting a site bloated and slow and very unorganized is easy. Go to a professional developer and ask for advice, you will not regret later… or think about using a hosted solution, which will leave all this to the hosting company but will give you less flexibility in terms of customization.
This happened to a website in Australia, a beautiful country with great people that I have in my heart, so I was very pleased that I was able to help them.
WordPress is a very complete, complex and still easy platform to work with that can provide professional results with a few clicks and free plugins. Many people think that for this reason, it’s “ok” to get the job done by themselves or with a cheap company.
A professional removal service tailored like this one I did costs a lot of money, between 500 and 1.5k, and it’s not always guaranteed that the results will be 100% accurate …
So think first about it when you want to cut costs on security.
I would say that getting a site bloated and slow and very unorganized is easy. Go to a professional developer and ask for advice, you will not regret later… or think about using a hosted solution, which will leave all this to the hosting company but will give you less flexibility in terms of customization.
This happened to a website in Australia, a beautiful country with great people that I have in my heart, so I was very pleased that I was able to help them.
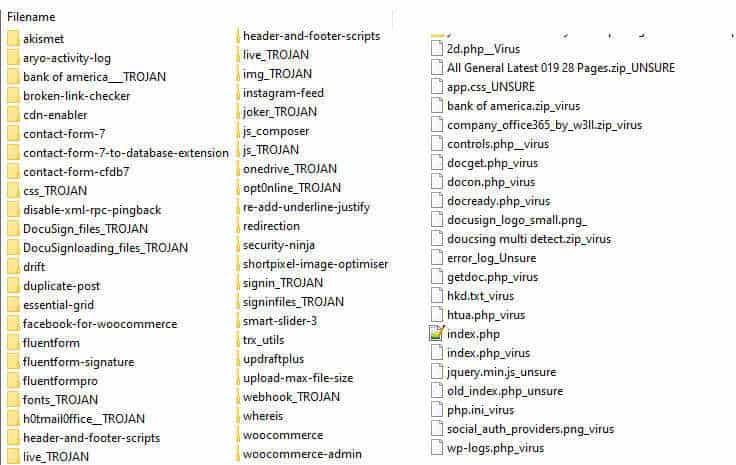 After Checking the “fake” directories and the Trojan ones, plus the virus files we also had to secure the data.
To avoid that any potential virus files would break the site, I had to test one by one the folders into the plugins dir to make sure it won’t lead to any further damage.
Also, I had to cut the “loop” where the site was continuously re-attempting to create the dirs and the backdoor over and over, which kept getting the site “hacked”.
It was No Joke!
Lastly, we had to troubleshoot the WP-ADMIN dashboard as some functions were corrupted and some buttons were not fully operational leading to a broken admin dashboard.
Updating the site theme along with some extra security measures and installation of a WP security plugin helped the site to have a ZERO downtime and a full recovery.
We had to keep it under testing and we’re still doing it now but, fingers crossed, I was able to avoid a complete “rebuilt” of the site or, more importantly, loss of precious, valuable data.
After Checking the “fake” directories and the Trojan ones, plus the virus files we also had to secure the data.
To avoid that any potential virus files would break the site, I had to test one by one the folders into the plugins dir to make sure it won’t lead to any further damage.
Also, I had to cut the “loop” where the site was continuously re-attempting to create the dirs and the backdoor over and over, which kept getting the site “hacked”.
It was No Joke!
Lastly, we had to troubleshoot the WP-ADMIN dashboard as some functions were corrupted and some buttons were not fully operational leading to a broken admin dashboard.
Updating the site theme along with some extra security measures and installation of a WP security plugin helped the site to have a ZERO downtime and a full recovery.
We had to keep it under testing and we’re still doing it now but, fingers crossed, I was able to avoid a complete “rebuilt” of the site or, more importantly, loss of precious, valuable data.
 I was pleased to also receive very positive feedback from the hosting company itself regarding my work, which was appreciated and recognized as a valuable one.
As a bonus, we also had the email address that was receiving the data from the Scam-Created site along with the Hacking team connected (maybe… this info is never trustworthy as there are internal rivalries) and reported to whom it concerns for further investigation.
A few steps that I followed:
I was pleased to also receive very positive feedback from the hosting company itself regarding my work, which was appreciated and recognized as a valuable one.
As a bonus, we also had the email address that was receiving the data from the Scam-Created site along with the Hacking team connected (maybe… this info is never trustworthy as there are internal rivalries) and reported to whom it concerns for further investigation.
A few steps that I followed:
- Secure your site. If your site gets hacked, make sure you put it under maintenance and contact a professional developer / security consultant or company. There are companies like Sucuri and Astra that offer a cleaning and malware removal scan service. They also give you a firewall that will help your site run securely and under control. These services are not cheap, but they will save your site probably and this means your business and further loss later. Don’t think, “I can do it by installing a plugin or a WordPress firewall”, it won’t work. Simple as that.
- Change WordPress Salt Keys. These keys are created automatically when a WordPress instance is installed and keep the connection open (like a cookie) so changing them will log out ALL currently logged-in users (including bots, hackers, etc.) and you will be able to take it from there.
- Check the FTP files. The index files, the upload folders, and the plugins directory and theme directory. Scan for any “strangely” named file or dir that you don’t recognize. WordPress plugin folders and files have mostly the same name as the plugin so you can probably troubleshoot it. For the “suspect” files, download and open with a text / code editor and see what’s inside to make sure it’s not a virus. DON’T DELETE the files as you may trigger a chain-reaction that could delete the full site or inform the hacker. Tag the files on a note.
- Change the URL admin and login URL. This is not always a “shared” approach and has some fallbacks, but there are plugins out there that can help with this and work pretty well. If not you can also manually use the .htaccess file to get the job done.
- Track errors on the dashboard or site if there are any. Write down and take a note of them so you can troubleshoot later or provide a professional with the logs.
- Change into the Wp-Config file the database access passwords. If the hackers could log in to the site and put some files into the root, and the wp-config was there, there is a big chance they could also download it and take advantage to re-inject later also with an SQL query.
- Secure the XML-RPC. Or use a plugin to temporarily disable its use if you don’t need it.
- Add strict rules. Ensure there are some strict rules into the htaccess regarding allowed files upload type. We have to remove any handlers for files in the uploads folder so that an interpreter can’t run an uploaded file. Note that for certain file extensions it’s best to force them to be interpreted by Apache as plain text for an extra layer of security.
- Block and keep under control IP addresses that hammer your site. This is a partial thing as with VPN it’s easy to avoid this measure, but as many hackers run bots, this may temporarily give us time to fix the site in the meanwhile. Using Wordfence with their built-in blocker firewall is good.
 WordPress is a very complete, complex and still easy platform to work with that can provide professional results with a few clicks and free plugins. Many people think that for this reason, it’s “ok” to get the job done by themselves or with a cheap company.
A professional removal service tailored like this one I did costs a lot of money, between 500 and 1.5k, and it’s not always guaranteed that the results will be 100% accurate …
So think first about it when you want to cut costs on security.
I would say that getting a site bloated and slow and very unorganized is easy. Go to a professional developer and ask for advice, you will not regret later… or think about using a hosted solution, which will leave all this to the hosting company but will give you less flexibility in terms of customization.
This happened to a website in Australia, a beautiful country with great people that I have in my heart, so I was very pleased that I was able to help them.
WordPress is a very complete, complex and still easy platform to work with that can provide professional results with a few clicks and free plugins. Many people think that for this reason, it’s “ok” to get the job done by themselves or with a cheap company.
A professional removal service tailored like this one I did costs a lot of money, between 500 and 1.5k, and it’s not always guaranteed that the results will be 100% accurate …
So think first about it when you want to cut costs on security.
I would say that getting a site bloated and slow and very unorganized is easy. Go to a professional developer and ask for advice, you will not regret later… or think about using a hosted solution, which will leave all this to the hosting company but will give you less flexibility in terms of customization.
This happened to a website in Australia, a beautiful country with great people that I have in my heart, so I was very pleased that I was able to help them.